Abstract:
This study analyzes the 2025 Louvre Museum jewel heist as a case of strategic failure in physical and intelligence security. It explores operational methods, vulnerabilities, and implications for global security practices and institutional resilience. Lessons are drawn for corporate security, intelligence analysis, and cyber-physical integration.
Keywords: Louvre Heist, Intelligence Analysis, Physical Security, NATO, Commodity Theft, Cybersecurity
Eight Minutes at the Louvre: A Case Study in Global Security Vulnerabilities and Strategic Response
Dr. Cihan AYDINER
Executive Summary
On October 19, 2025, the Louvre Museum in Paris was the target of a meticulously planned jewel heist. In just eight minutes, a group of thieves disguised as construction workers stole royal jewelry of incalculable worth from the Galerie d’Apollon (Granados & Shao, 2025). This case study analyzes the operational method, security failures, historical context, and implications for homeland and corporate security, offering insights for professionals and students in intelligence, risk management, and physical security integration.
Incident Overview
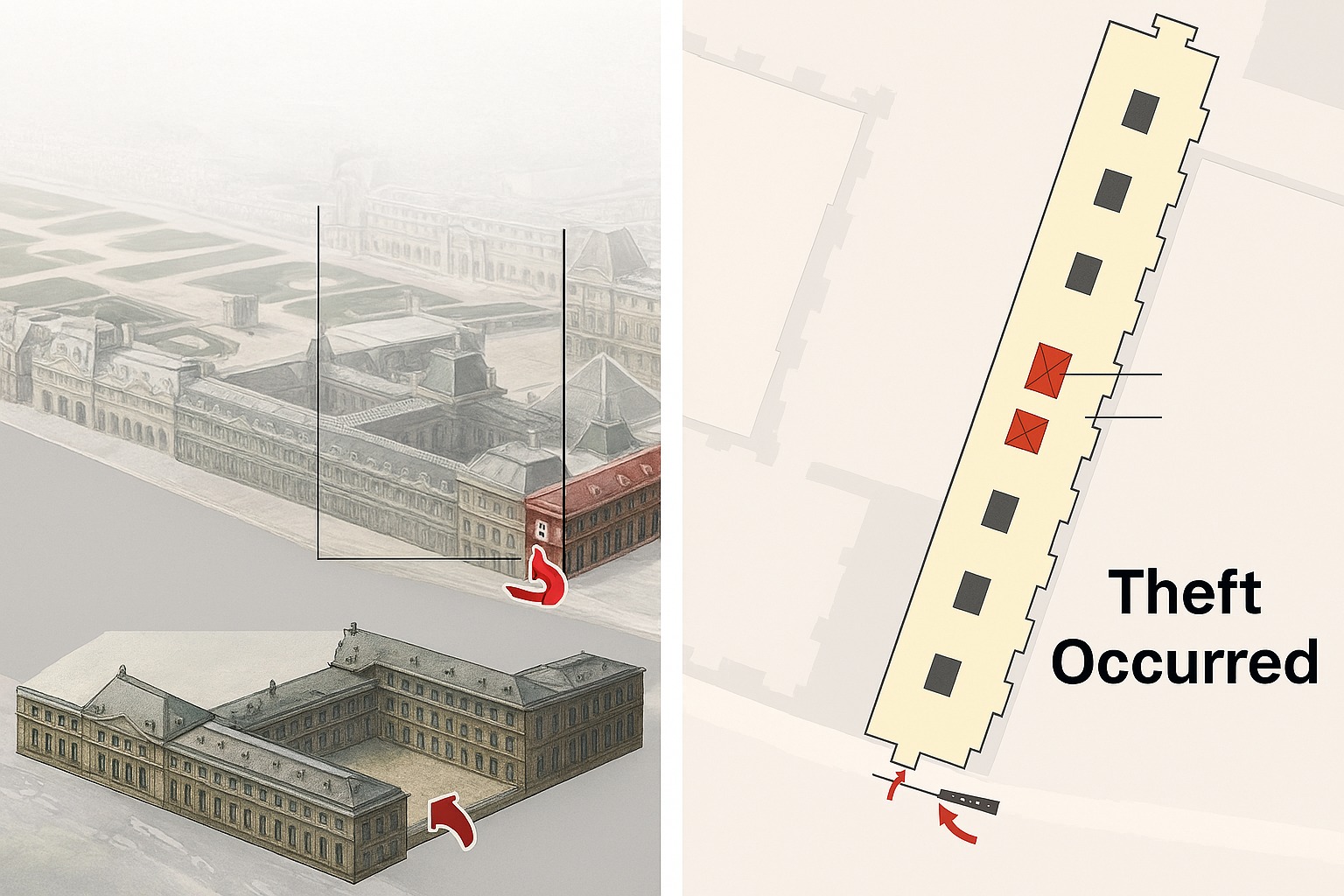
Created by Microsoft Copilot
Illustration of the 2025 Louvre Museum jewel heist, showing the entry point via truck-mounted ladder, escape route, and security vulnerabilities. Designed for educational use in global security, intelligence analysis, and physical security integration.
At 9:30 a.m., a truck equipped with an electric ladder (monte-meubles) was parked beneath the Apollo Gallery. The thieves ascended the ladder, used a disc cutter to carve through the window glass, and triggered the alarm.

Image modified using SORA
Depicts law enforcement presence at the suspected entry point used by the thieves. This image has been digitally enhanced to highlight the operational zone and security response.
They threatened guards, smashed display cases, and stole a royal sapphire necklace, a royal emerald necklace, and Empress Eugénie’s diadem.

Photo: David Liuzzo, Wikimedia Commons
This crown, part of the French Crown Jewels, was dropped and damaged during the thieves’ escape from the Louvre. It contains over 1,300 diamonds and emeralds and was recovered near the museum’s perimeter.
By 9:38 a.m., they escaped on high-powered scooters. The crown of Empress Eugénie was dropped during the escape and later recovered, damaged.

Photo: Ezgi Deliklitas, Unsplash
The Galerie d’Apollon houses France’s Crown Jewels. The thieves accessed this gallery via a truck-mounted ladder and targeted display cases containing royal jewelry.
Security Failures and Key Vulnerabilities
Post-incident audits revealed incomplete surveillance coverage (25–40% blind spots), outdated infrastructure, understaffed teams, and weak contractor vetting. These vulnerabilities mirror patterns seen in similar museum thefts in Berlin, Oslo, and Oxford.
Commodity Theft Versus Art Crime
Unlike traditional art theft driven by prestige or ransom, commodity theft targets raw materials for quick resale. Jewelry offers anonymity and liquidity, making recovery and traceability difficult.
Lessons in Physical Security Integration
Best practices include layered physical security, ongoing staff training, contractor vetting, cyber-physical integration, and red team exercises to identify weaknesses.
Intelligence Analysis: Applying the Intelligence Cycle
Effective museum security requires intelligence-driven operations. The intelligence cycle; planning, collection, processing, analysis, dissemination, evaluation, supports proactive threat management (ASIS International, n.d.).
Pre-Incident Indicators
Signals included unusual contractor access, social media chatter, staff complaints, and anomalous tool purchases.
Fusing Intelligence with Security Operations
Museums benefit from threat fusion centers, scenario planning, and AI analytics to detect behavioral shifts and penetration risks.
Lessons for Security and Intelligence
- Layered Defense and Infrastructure Resilience
- Insider Threat Mitigation (e.g., behavioral analytics, access control audits).
- Intelligence-Driven Security Operations
- Realistic Training and Multi-Agency Coordination
Strategic Discussion Questions for Security Audiences
- Which security upgrades would most effectively have prevented the Louvre heist?
- How can security professionals adapt museum security lessons to critical infrastructure?
- What protocols detect insider threats across alliances?
- What are best practices for integrating OSINT, HUMINT, and SIGINT in museum or infrastructure security?
- How does AI enhance surveillance and response?
Pedagogical Value and Discussion
This case offers a holistic view for students and educators, emphasizing risk management, intelligence coordination, and adaptive security strategies.
References
- ASIS International. (n.d.). The six steps in the intelligence cycle.
Baumeister, M. (n.d.). Louvre Museum [Photograph]. Unsplash. https://unsplash.com/photos/people-gathering-near-louvre-museum-during-daytime-GCfE4fl7tIQ - Deliklitas, E. (n.d.). Louvre Museum [Photograph]. Unsplash. https://unsplash.com/photos/theceiling-of-a-building-with-paintings-on-it-fyx6IVZEeYI
- Demes, K., Rojas, L., & Tanaka, M. (2024). Challenges requiring new thinking in museum security.
- Granados, S., & Shao, E. (2025, May 15). How the Louvre jewelry heist unfolded. The New York Times. https://www.nytimes.com
- Hirsch-Gallagher, C. J. (2024). Defensible collections: Designing a safe exhibit space. PEAS Journal.
- Liuzzo, D. (n.d.). Louvre Museum [Photograph]. Wikimedia Commons. https://commons.wikimedia.org/w/index.php?search=louvre+museum%2C+crown+of+empress+eugenie&title=Special%3AMediaSearch&type=image
- Microsoft Copilot. (2025). Illustration of the 2025 Louvre Museum jewel heist [AI-generated image].
Dr. Cihan Aydiner is an Assistant Professor and program director of Homeland Security at Embry-Riddle Aeronautical University Worldwide (ERAU-W). He has had prior academic and professional roles at Louisiana State University, Hybridcore (an AI-Powered Decision-Making Company), and Army. He has doctoral and master’s degrees in Sociology from Louisiana State University and a master’s degree in National and International Security Management from Army War College. He has many funded grant projects, publications, documentary films, and technical reports. Dr. Aydiner’s current research focuses on the complex interdependencies among policy, homeland security, and international migration.






